Important update: extended deadline
We've extended the deadline for fixing warnings caused by third-party code to May 4, 2021. This is to allow our partners more time to ensure that all warnings have been resolved before we switch off the jQuery migration plugin.
Mono is rolling out an important security improvement that affects all live websites built with the Mono Editor (versions II and V5).
What’s changing?
We’re updating the jQuery library on all live websites from version 2.1.3. to the latest version, 3.5.1. jQuery is a JavaScript library that is used mainly for manipulating CSS and for performing HTML events. It is used in many of the interactions visitors can perform on a website built with the Mono Editor, for example when they click the location pin on a Map module or select a time slot on the Scheduling wizard.
Why this change?
jQuery 2.1.3 has a few known security vulnerabilities mostly related to Cross-site Scripting (XSS). For the same reason, the Google Lighthouse report flags this as a warning and penalizes the website by reducing its Best Practises metric.
jQuery 3.5.1. has no known security vulnerabilities at this point and, as a bonus, will make a Mono-built website score a full 100 in the Best Practises metric.
Do I need to do anything?
We’ve made sure that all native Mono modules, products and features are fully compliant with the new version of jQuery. If you have built websites entirely using native functionality and features in the Mono Editor and haven’t added any third-party scripts yourself, then you don’t need to do anything.
If you have added scripts on your own either through Global HTML, page-specific HTML or the HTML module, please read on.
What if I have added third-party scripts on my websites?
It’s important that you ensure that any code you’ve added yourself is able to work with jQuery 3.5.1. If parts of your code don’t comply, it may cause the embedded content to display wrongly or break altogether.
Although Mono is not responsible for any third-party code added to our platform, we want to do our best to help you transition to jQuery 3.5.1 to make your websites more secure. Therefore, we’ve added a jQuery migration plugin to all live sites for a temporary period of time. The plugin scans your website and logs violations in the browser console that need to be fixed. It also attempts to fix those violations so that your content displays correctly even if it isn't compliant with version 3.5.1. yet.
How do I spot violations?
To identify violations, open up a published website on your account, right-click any element on the page and select Inspect to open Chorme DevTools (most other browsers have similar tools) - or press Command+Option+C (Mac) or Control+Shift+C (Windows, Linux, Chrome OS).
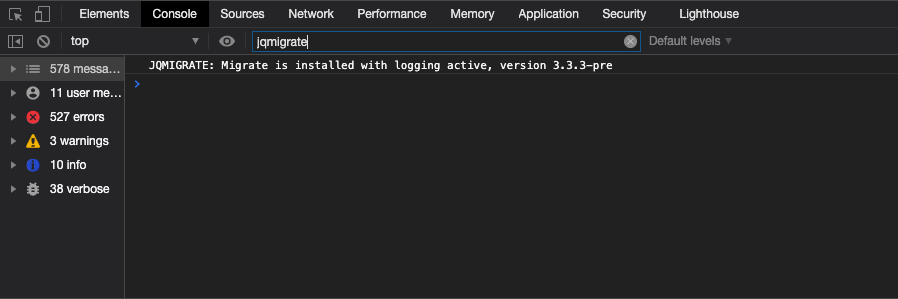
Click the Console tab and type in "jqmigrate" in the Filter input bar. If you see the message below, the jQuery migration plugin is running correctly on your website.
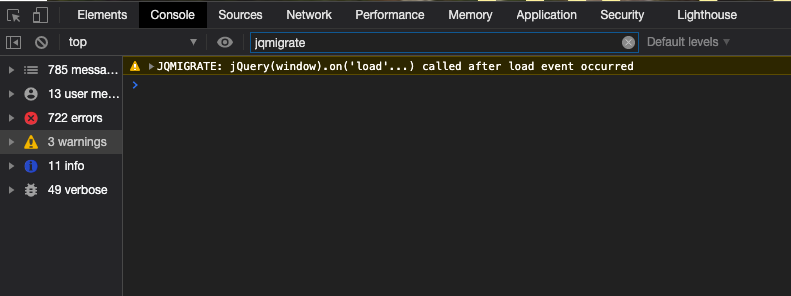
The plugin will log violations as you're browsing the website and performing interactions. It's recommended that you try out all the possible interactions on your embedded content. For example, try to open and close elements, expand dropdown menus, click buttons, and so on.
If the plugin detects any warnings, they will be listed in the console.
What if the plugin displays warnings?
If the jQuery migration plugin finds any issues that need to be resolved, please make sure to inform the author of the affect script(s) and ask them to fix them. It may be a good idea to send them a screen recording with the jQuery migration plugin running in the browser console.
A lot of useful information on fixing issues is also provided in jQuery's official upgrade guide. It may be beneficial to look up warnings found with the plugin in there.
Important dates
The jQuery 3.5.1. upgrade was released on January 14, 2021. This also includes the addition of the jQuery migration plugin.
On May 4, 2021 we’ll turn off the jQuery migration plugin. Please make sure that any third-party script warnings have been resolved by this date.